As you're obnoxious aware, everyone gets spam! Even with the best protection, some spam emails still slip through the cracks. But you can use applications or extra levels of defense that can help....
Read MoreFrom the Blog
- Cyber Security Awareness Training Series – Part I.II – Email (Spam)
- How to set up your signature in Outlook desktop (Window version)
- How to set up email signature in Outlook (Mac version)
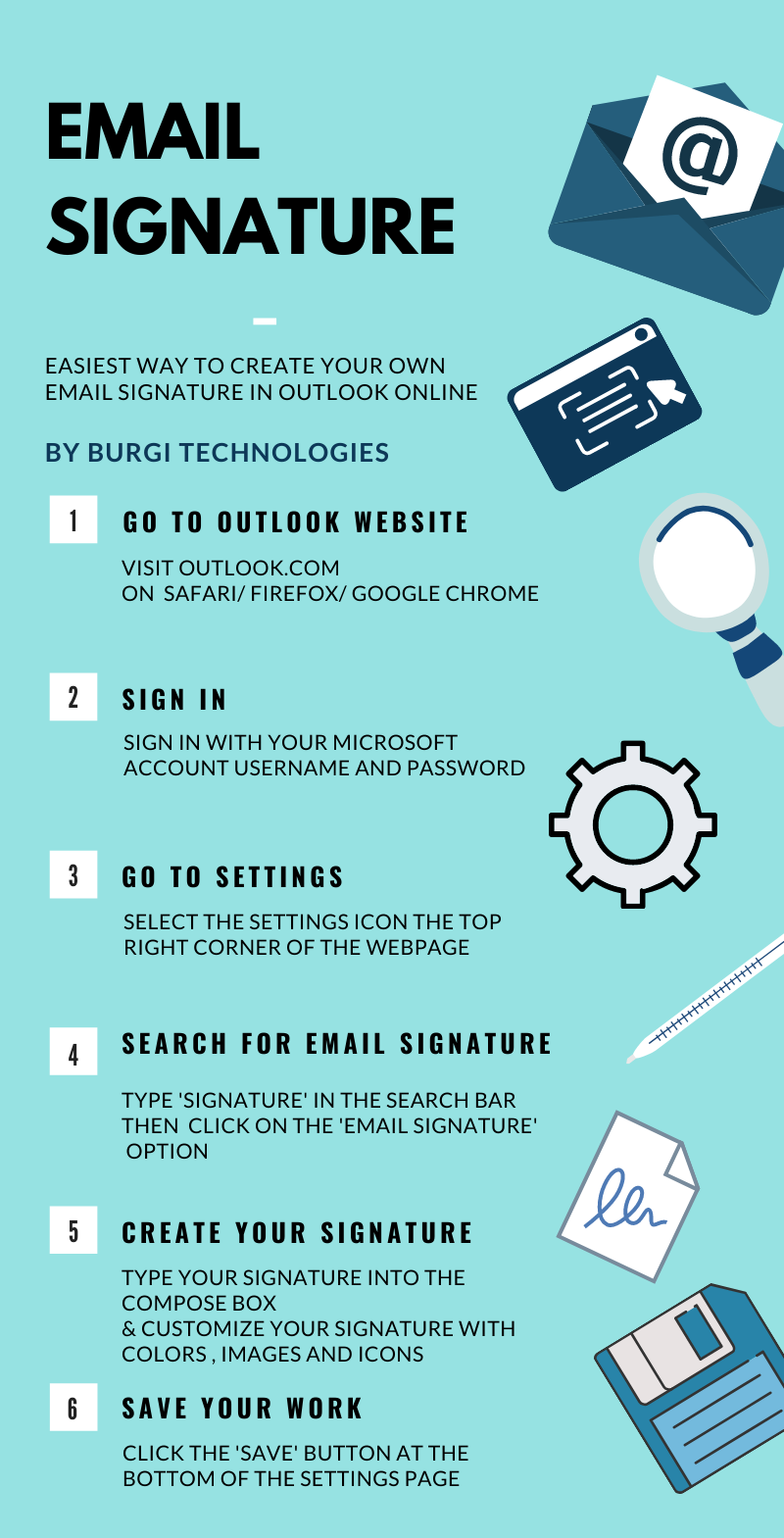
- How to set up your signature in Outlook Online
- Cyber Security Awareness Training Series – Part I.I – Email (Attachments)